VMware Enterprise PKS Management Console (EPMC) - Day 2

In the previous blog post we went through the Day-1 capabilities of the new version of the Enterprise PKS Management Console (EPMC). Let´s have a look at what´s in for Day-2.
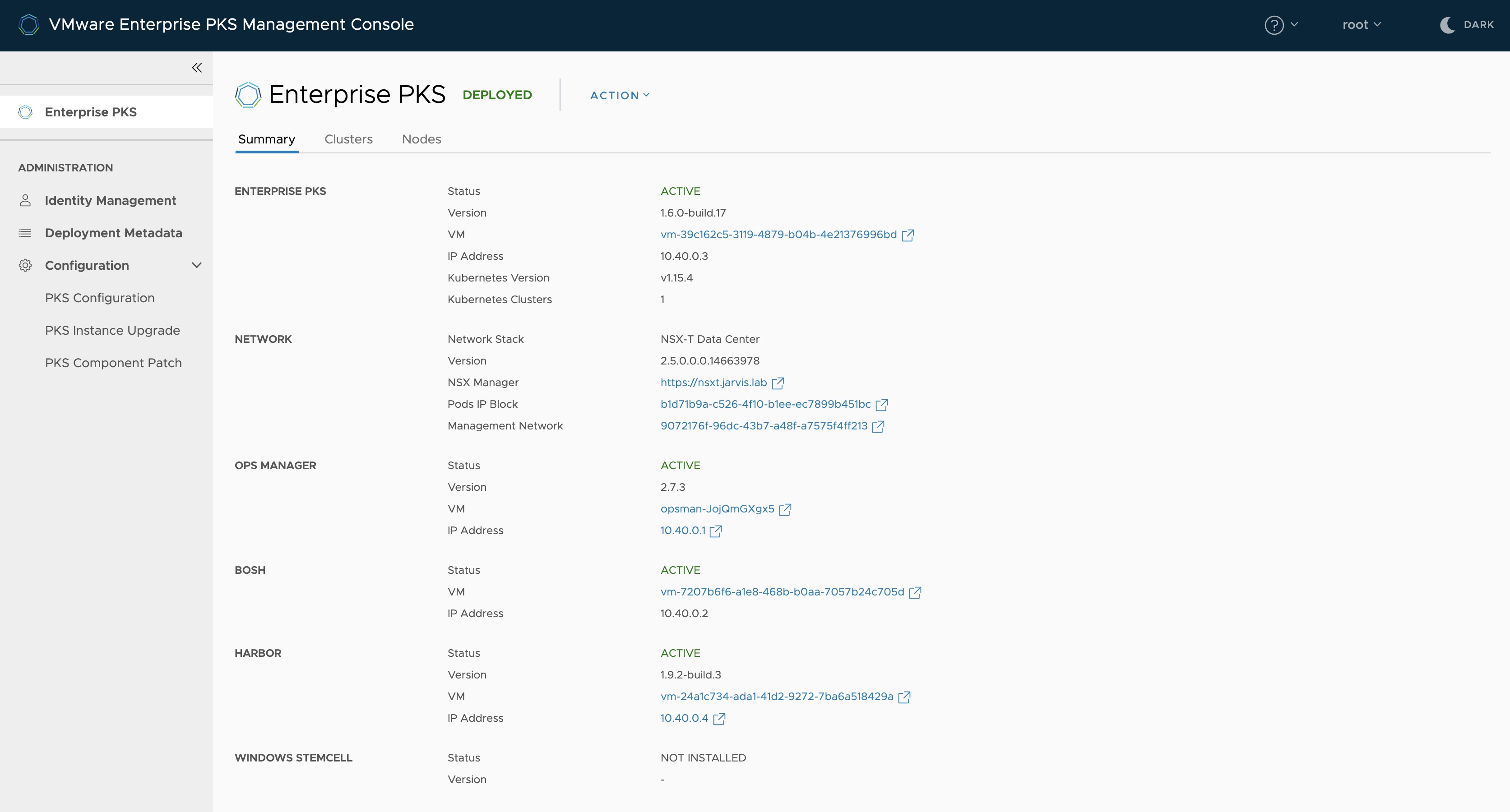
Summary Page
The summary page of your Enterprise PKS deployment will appear after clicking the Enterprise PKS button at the top left corner. This page will give you an detailed overview of all the PKS Management Plane components including important data like, Service State, Version Numbers, IP addresses and also Hyperlinks either to the relevant Virtual Machine in vSphere or to the Website of an Management-Component like, NSX-T or the Pivotal Ops Manager.
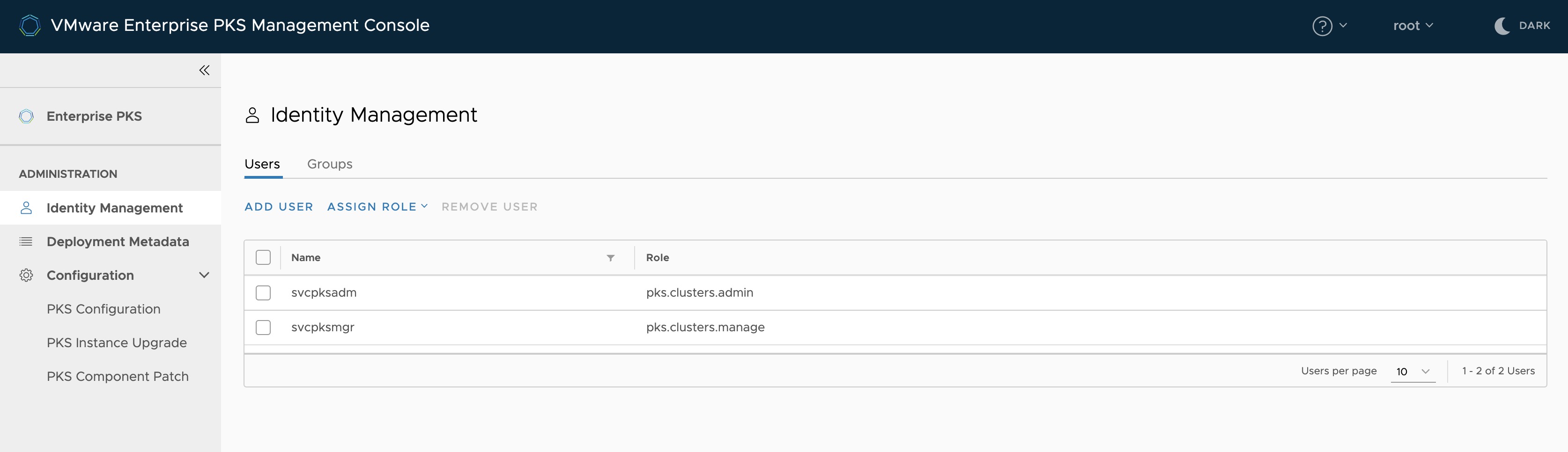
Identity Management
Do you remember the following?
uaac user add jarvis --emails jarvis@jarvis.lab -p Password0815With EPMC you can simply add users and groups through the Identity Management tab. Click on Add Users and fill out the required fields. In this version of EPMC, you cannot add individual LDAP or SAML users. Instead of, you have to use the Groups tab for LDAP or SAML authentication.
This release of Enterprise PKS Management Console does not support assigning roles to individual LDAP or SAML users. To assign roles to LDAP or SAML users, use user groups.
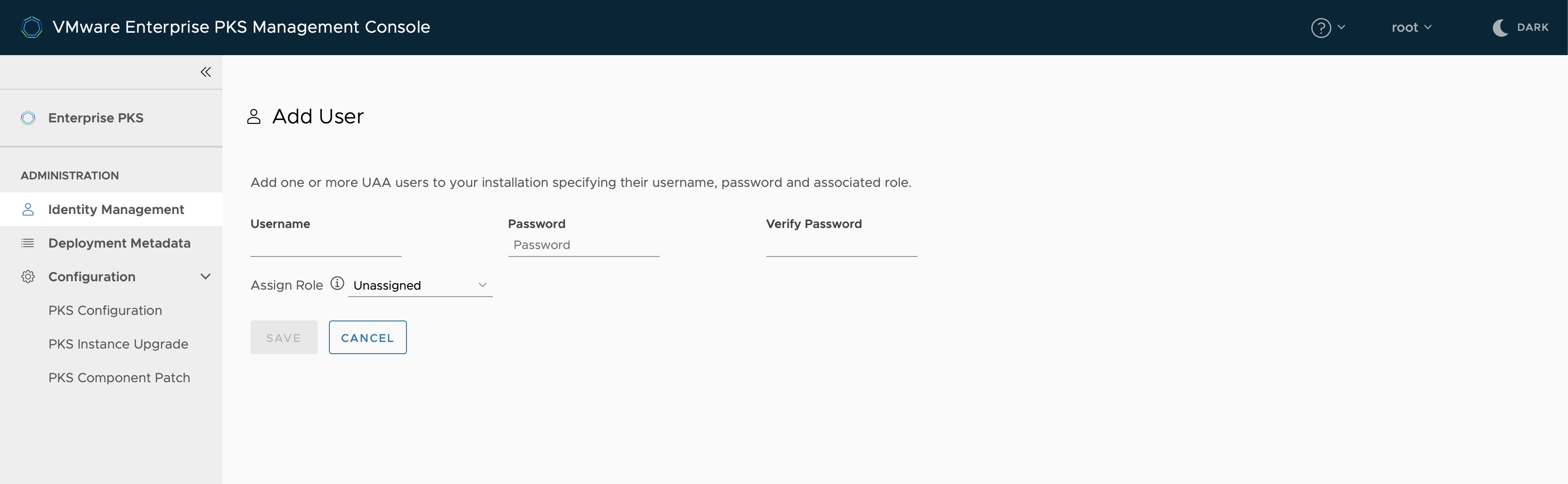
There are two roles which can be assigned. The Cluster Manager, to manage the lifecycle of the individual Kubernetes Clusters and the PKS Administrator, which manage the Enterprise PKS infrastructure.
Depending on what you have configured in Step 3 (Identity) during your deployment configuration, you can enter the distinguished name of an existing LDAP group (cn=,ou=,dc=) or the name of your SAML identity provider group.
Deployment Metadata
This section is kind of an “Documentation Page” for your Enterprise PKS deployment. You will find all the important Metadata beginning with IP-addresses, FQDNs, credentials (username & password), certificates up to the Enterprise PKS UAA Encryption Passphrase.
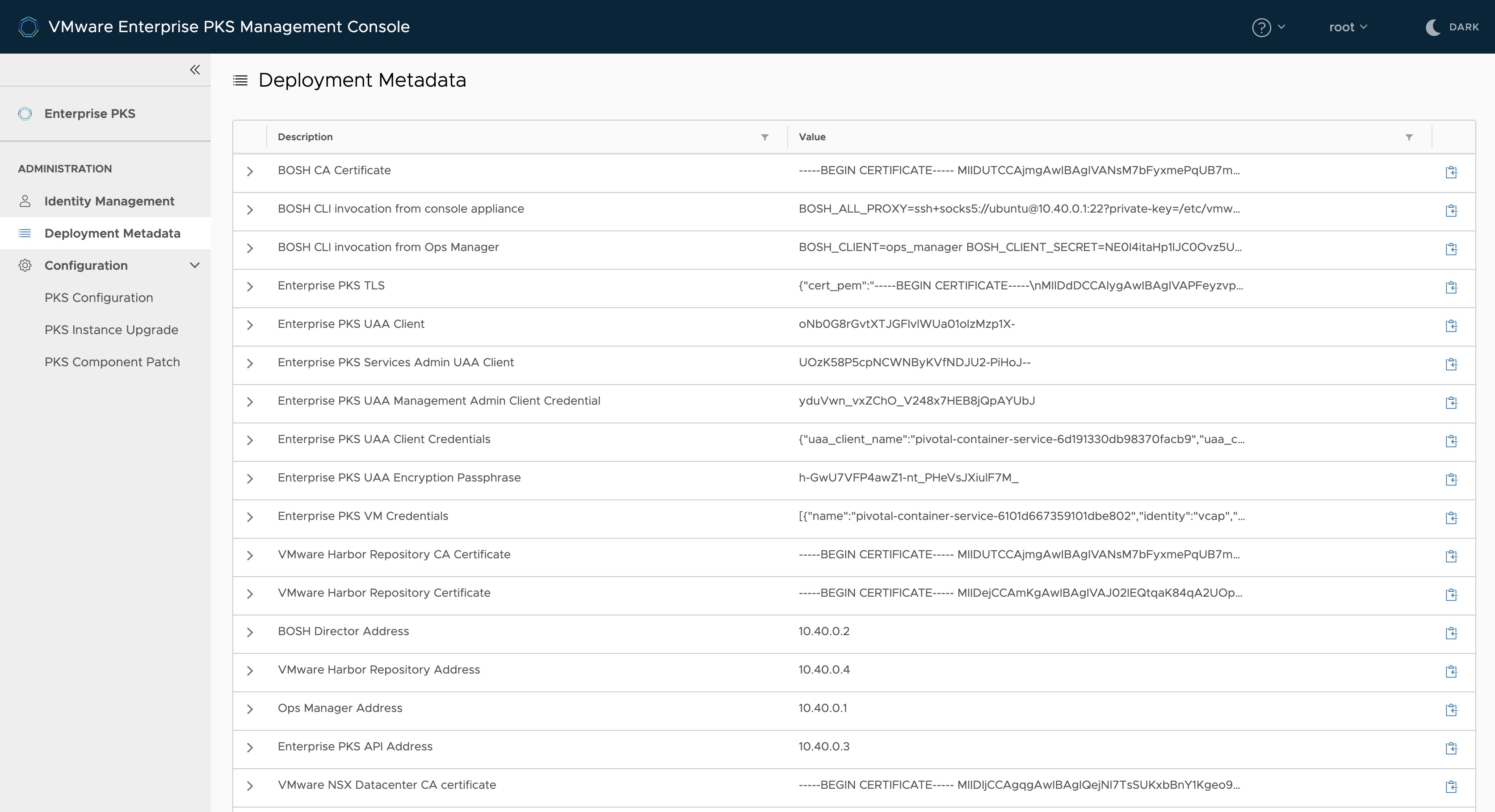
Just as an example what´s also in this section.
You can use the EPMC as a Jumphost for making use of the BOSH CLI to operationalise PKS. The necessary environment variables, which have to be exported, can be found in the Metadata section under the entry BOSH CLI invocation from console appliance, as you can see on Figure IV.
Once you have exported the environment variables, you can issue commands like:
bosh vmsto get the state of your deployment or
bosh tasks --recent=20to see the last 20 recent tasks of BOSH.
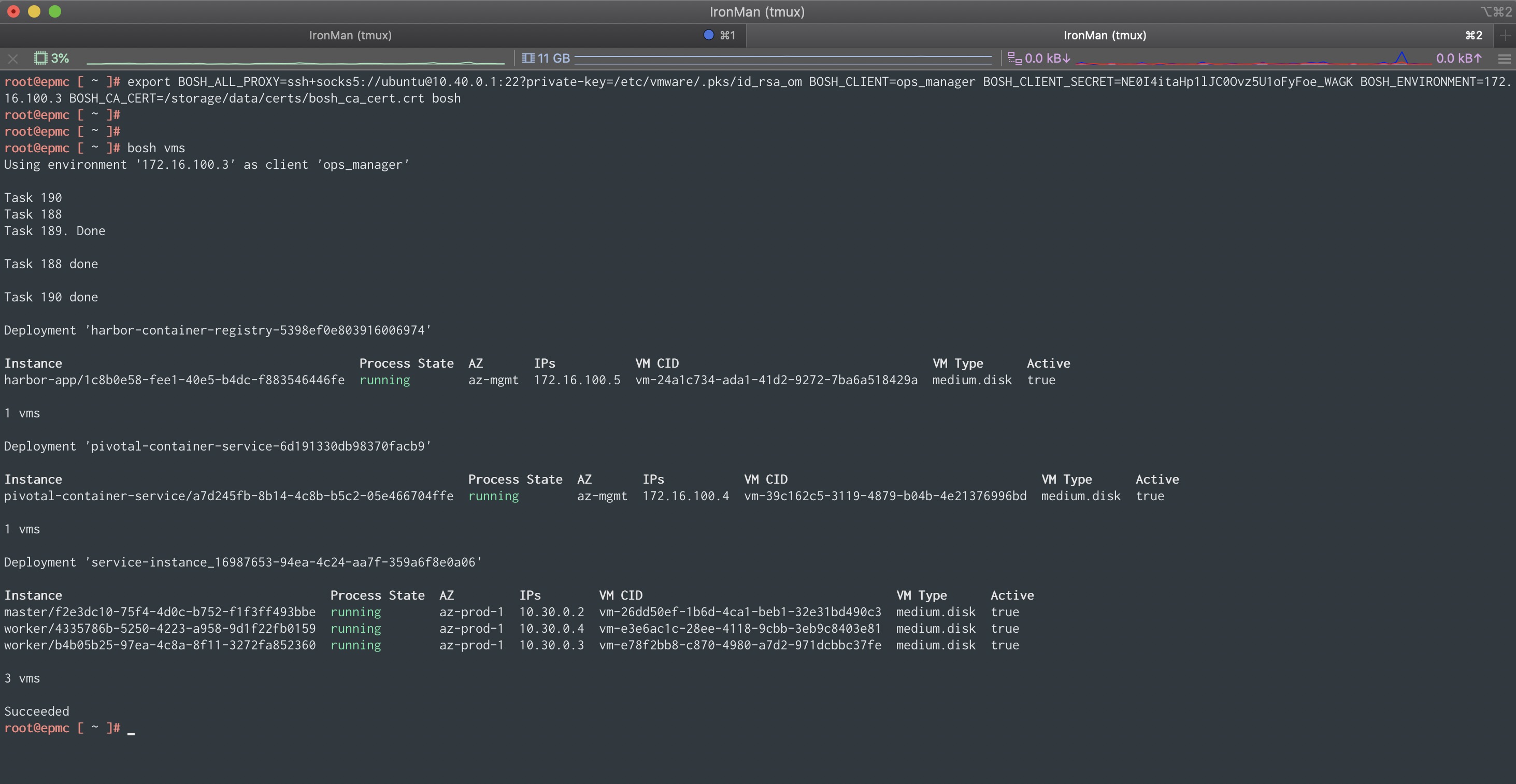
Kubernetes cluster creation
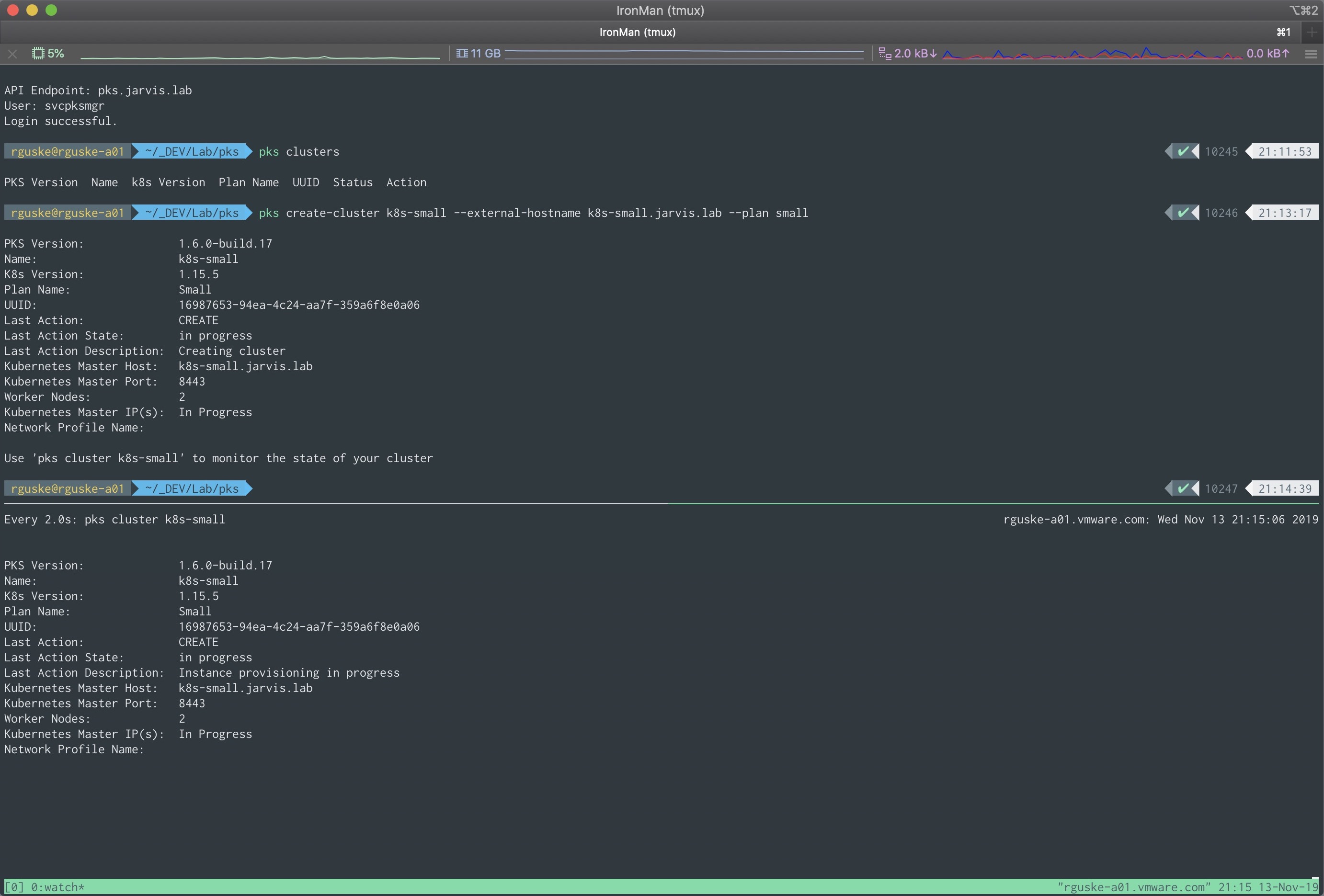
To create a new Kubernetes cluster in Enterprise PKS, you have to make use of the PKS CLI. Login into the PKS API Endpoint with a previously created user, which is in my example the svcpksmgr to which I have assigned the Cluster Manager role, and execute the following:
pks login -a pks.jarvis.lab -u svcpksmgr -p VMware1! --ca-cert pks.crt*After a successful login, create a new Kubernetes cluster in the desired “T-Shirt size” (--plan).
pks create-cluster k8s-small --external-hostname k8s-small.jarvis.lab --plan smallYou can use
watch -n 2 pks cluster k8s-smallto watch the creation-progress of your new K8s-cluster.
Kubernetes cluster information
Again! The Enterprise PKS Management Console brings tons of benefits to operators, by beeing the single pane of glass for your Enterprise PKS/ your Kubernetes environment. The following screenshot gives you an idea what I mean.
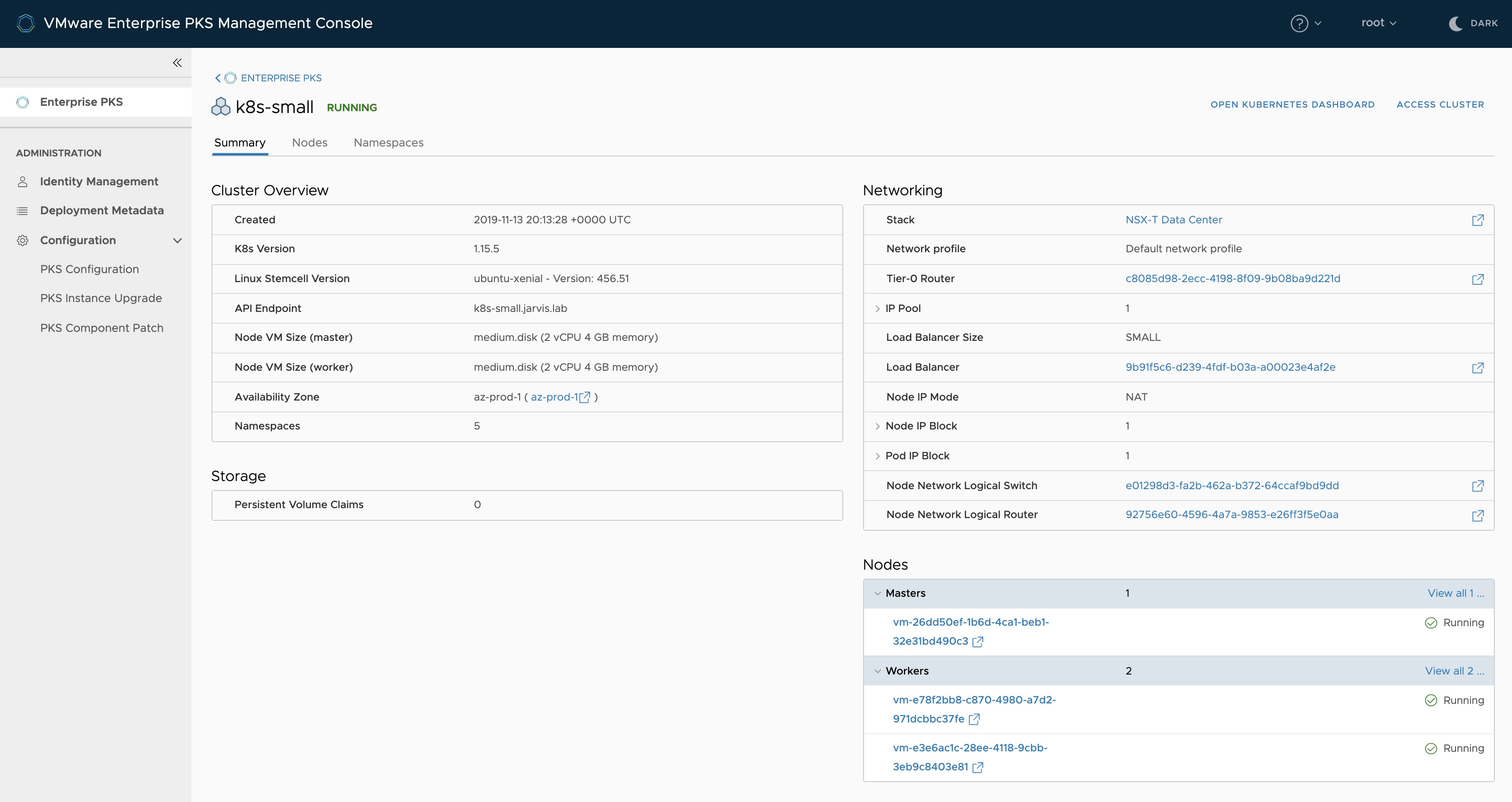
You can see, that besides the creation date of your cluster, the version of it, the count of Master, Worker and Namespaces OR Storage related information, it also shows you all relevant details regarding Networking like: the assigned Network Profile, the connected T0 and T1-Router, the Logical Switch, Load Balancer information as well as Node and POD networking data.
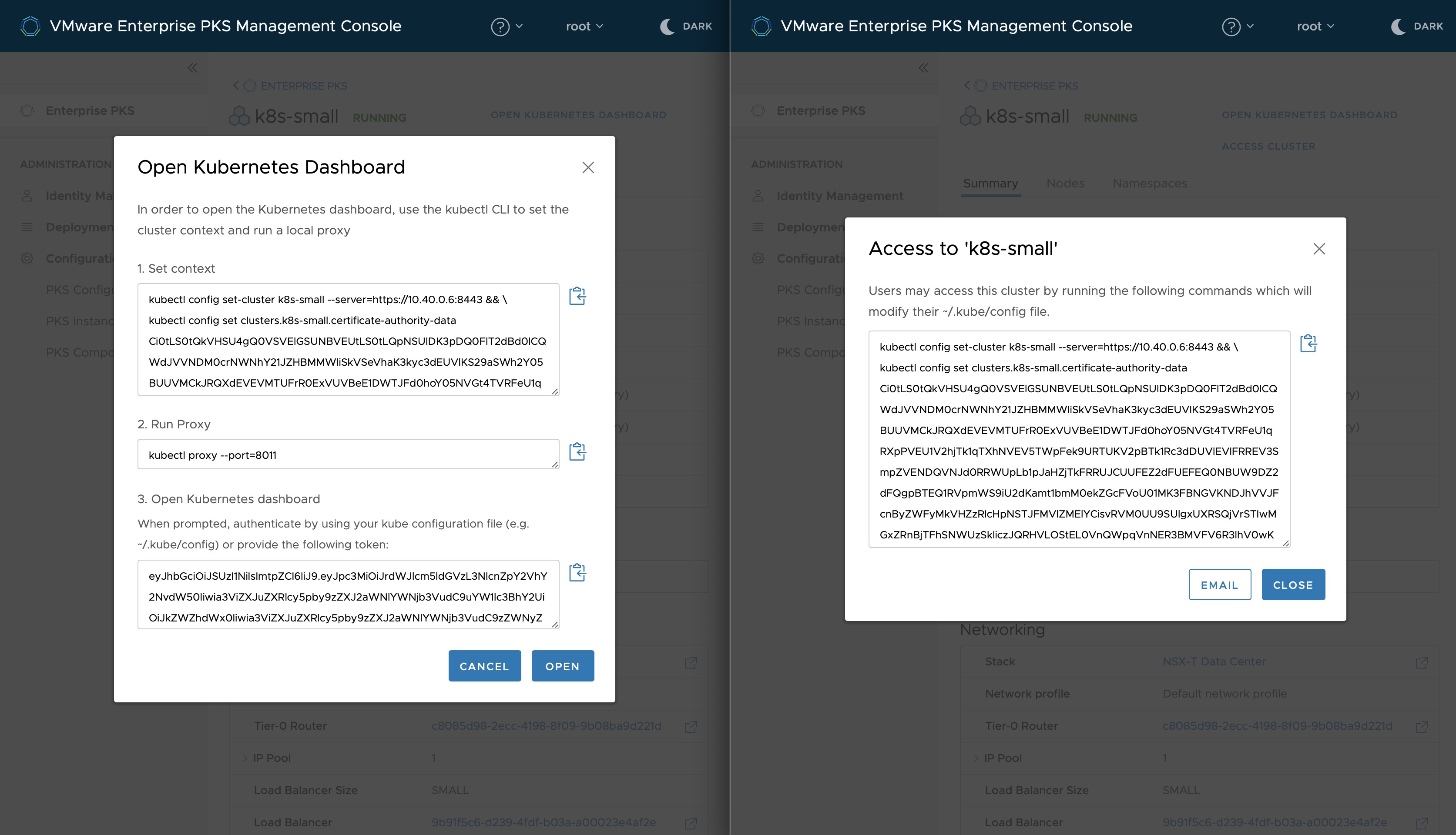
By selecting Open Kubernetes Dashboard or Access Cluster, a new window appears in both cases with the necessary command-lines in it, which you can either use to get access to the K8s-Dashboard or the Cluster. Otherwise, you can pass it on to the colleague who is eagerly waiting for it.
If you have multiple Kubernetes clusters across multiple Availability Zones deployed, you will get the right synopsis on the Nodes tab.
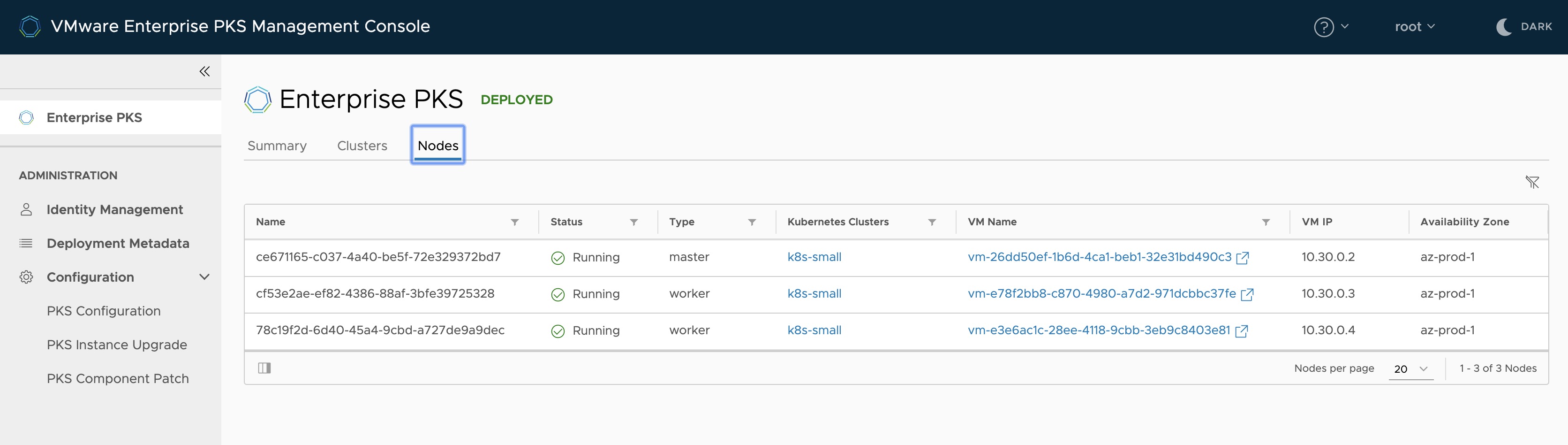
Having an understanding of how Enterprise PKS works with NSX-T is crucial. I don´t want to stress this out here, but as a reminder:
Each Logical Switch will have a Tier1 Logical Router as a Default Gateway. For the Tier1-Cluster Router, the first available subnet from Nodes-IP-Block will be used with the first IP address as the Default Gateway.
For all Kubernetes Name Spaces, a subnet will be derived from the Pods-IP-Block A SNAT entry will be configured in the Tier0 Logical Router for each Name Space using the IP-Pool-VIPs since it is the Routable one in the enterprise network.
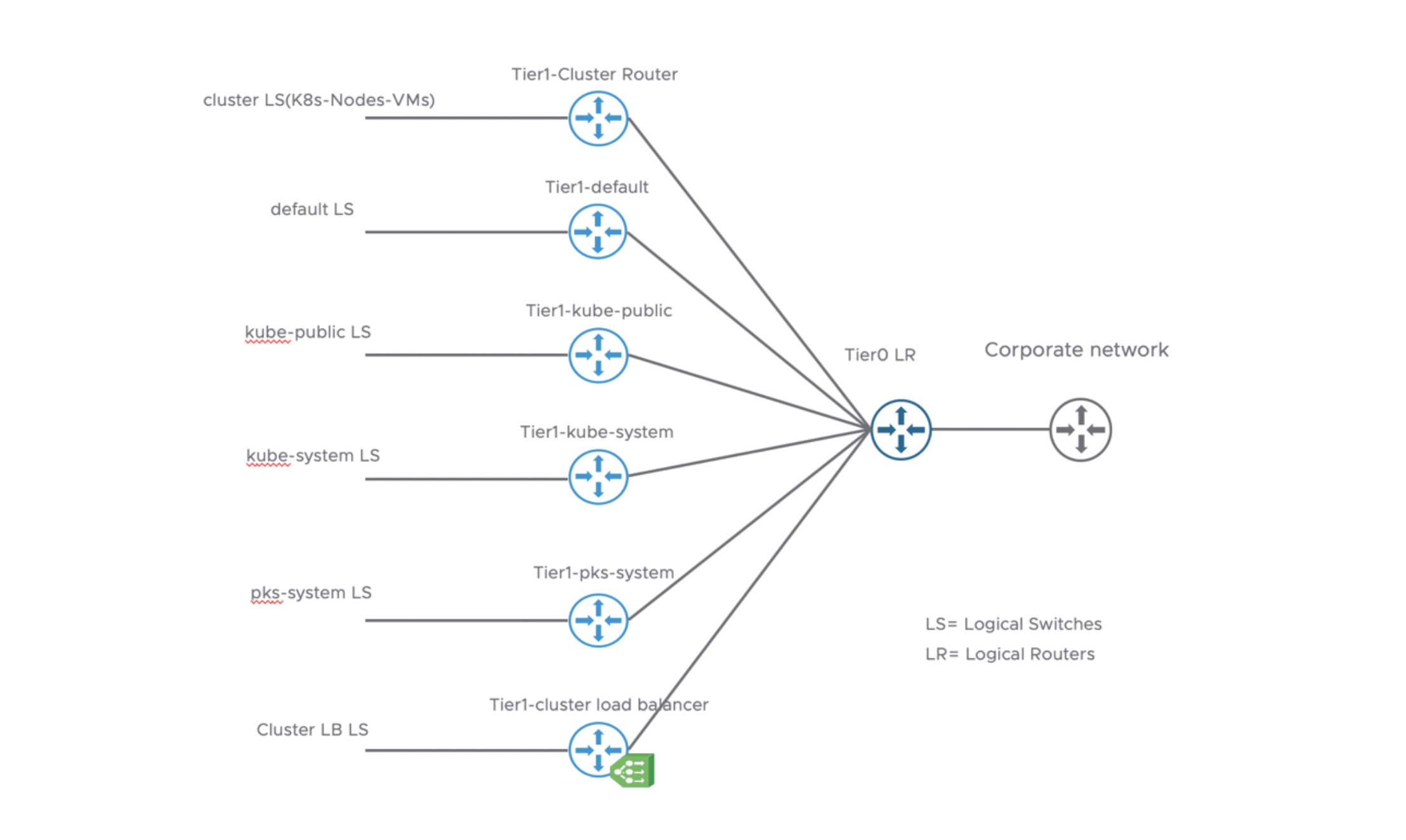
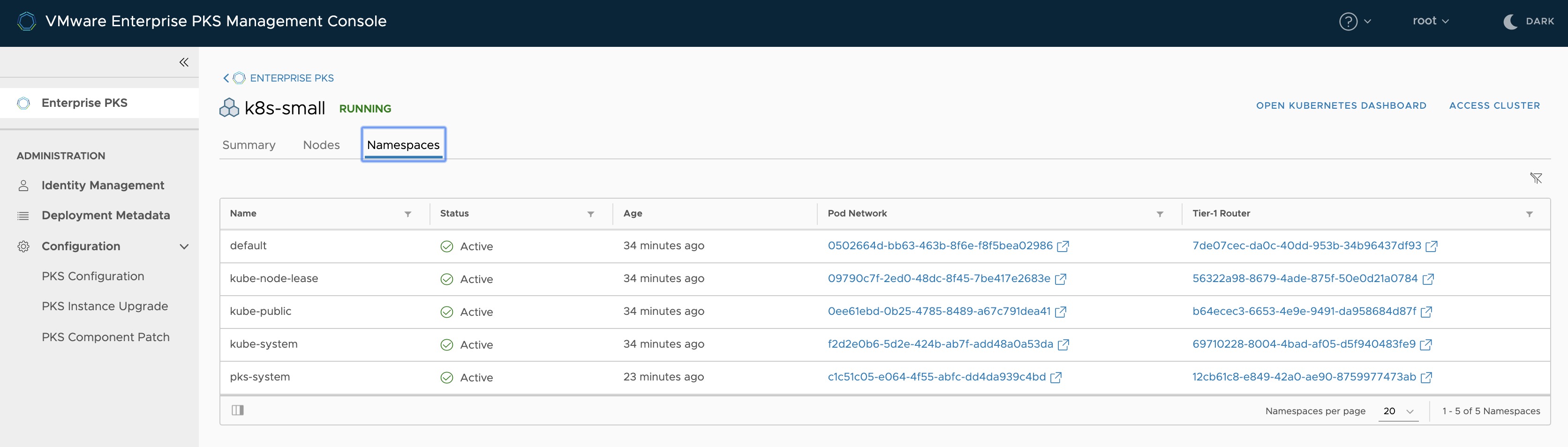
The Namespace tab provides you the Hyperlinks to the NSX-T Logical Switches (POD Network) as well as the T1-Router were all the Kubernetes Namespaces are connected to.
Upgrade Enterprise PKS + Kubernetes
Upgrading your VMware Enterprise PKS Management Plane components as well as your Kubernetes cluster(s) can also be done via the EPMC. If a new version of PKS is available, you´ll be notified by a message at the top. But before you can run the upgrade, you have to migrate your deployment to the newer version of the EPMC first. Therefore:
- Download the new version via https://downloads.vmware.com
- Deploy the OVA
- If you deployed your old EPMC with a static IP and you would like to re-use it for the new version, just Shutdown the old appliance, reconfigure the vApp with a temporary IP address and Power on the appliance again (this should be done before rolling out the new one 😉)
- Login in into the new EPMC and select this time Upgrade. See Figure IV: Install or Upgrade Option
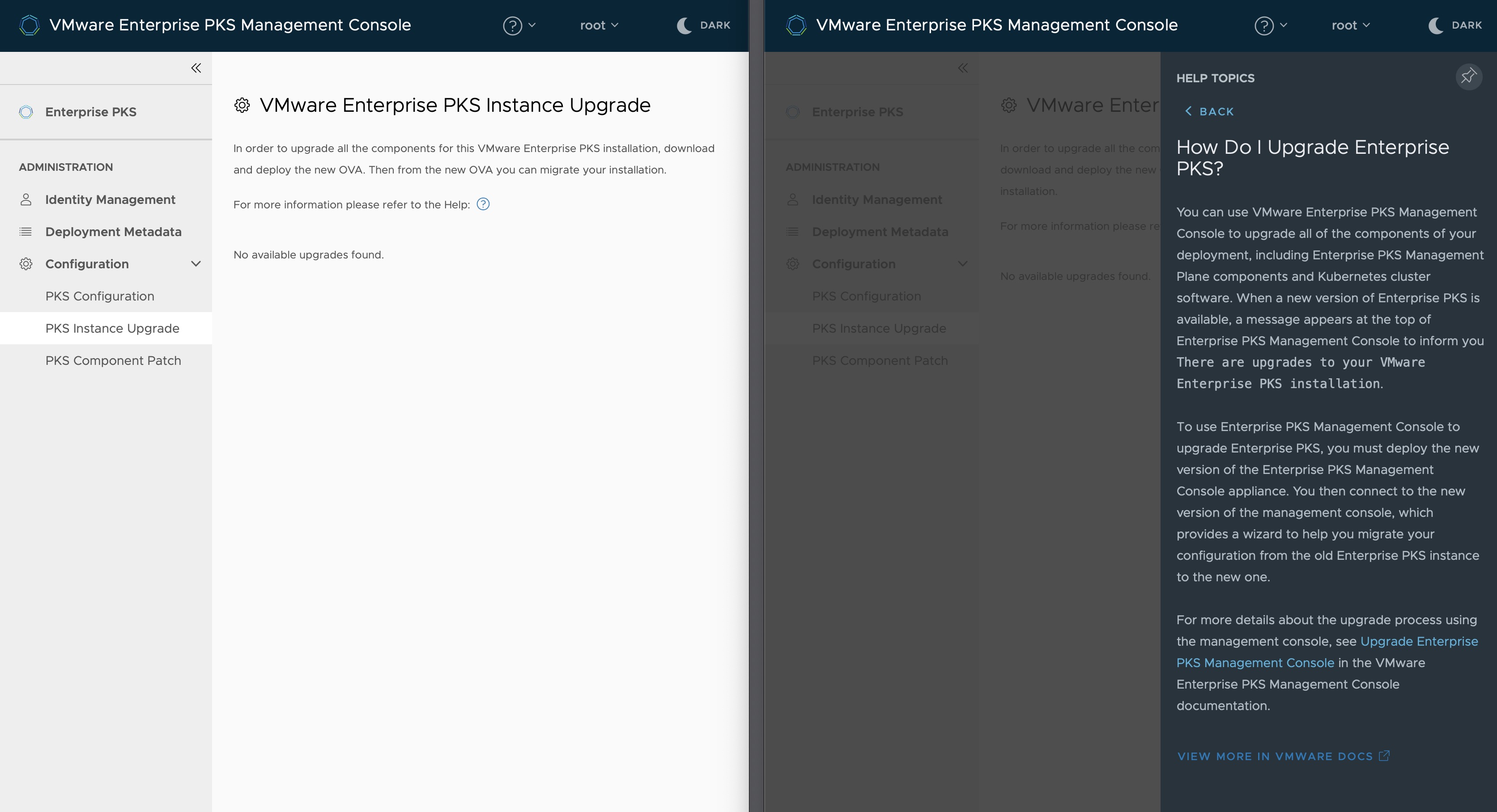
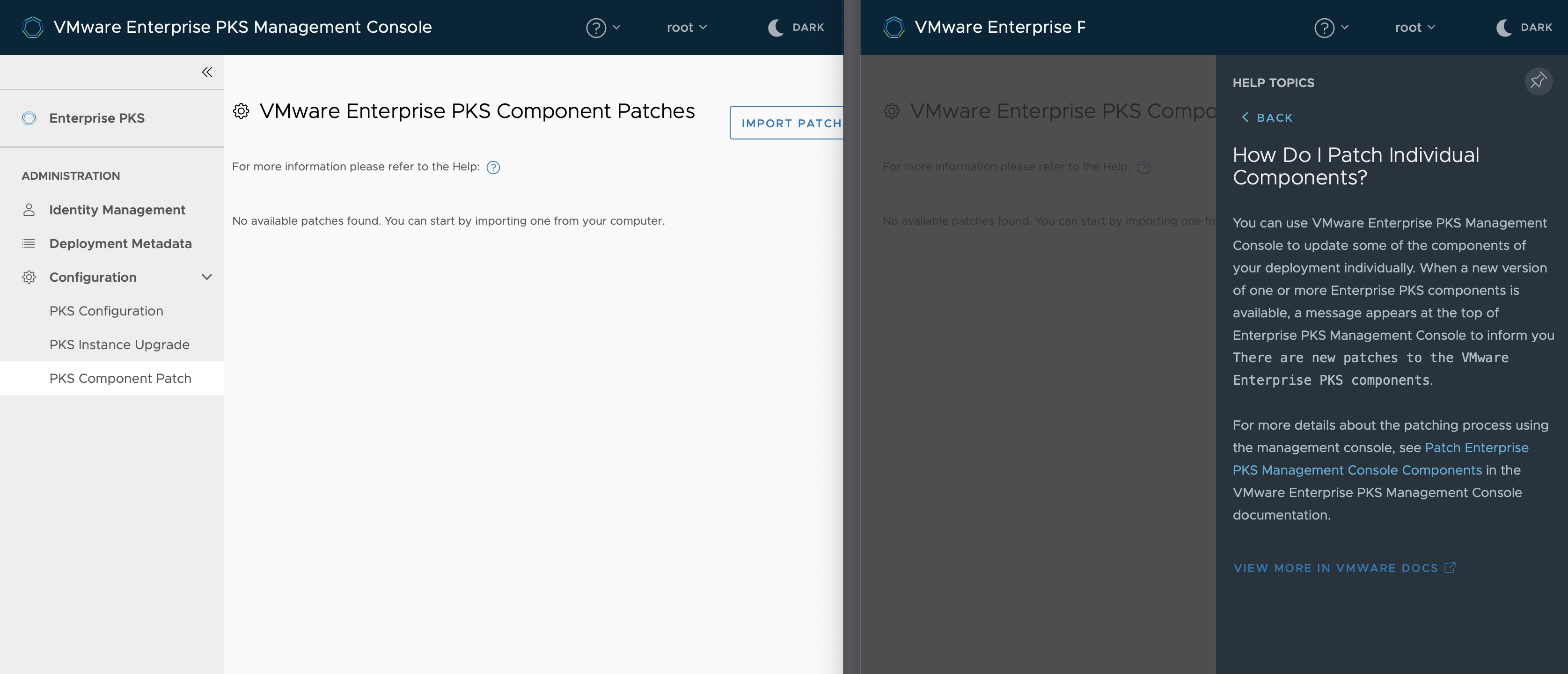
BTW: As you can see on the screenshot above and below, I´ve duplicated the tab of my browser to highlight a pretty neat feature of the EPMC. By clicking the ? icon, which can be found at the top bar as well as in some of the sections, a Contextual help will appear.
VMware Enterprise PKS Component Patches
Unfortunately, this section currently applies to the Enterprise PKS Management Console only. It´s planned to have the ability to patch the PKS Management Plane components in a future release too. For now applies, if an patch for the EPMC is available, you will be notified via a message at the top bar:
There are new patches to the VMware Enterprise PKS components.